CYBERSECURITY ASSESSMENT: GET STARTED
NIST 800-171 Compliance
Register for the 171Comply free cybersecurity assessment tool based on industry frameworks including the NIST Cybersecurity Framework to identify security concerns within your environment.
Your Guide to NIST 800-171 Compliance
Contractors for the Department of Defense (DoD) and other Government agencies must protect sensitive information from ever-increasing cybersecurity threats. Doing so requires implementing advanced cybersecurity solutions and following mandatory compliance requirements.
Contractors need clarity on what constitutes the minimum effective cybersecurity to protect Government data. The National Institutes of Standards and Technology (NIST) Special Publication (SP) 800-171 solves for this by identifying critical security best practices. The DoD and much of the Federal Government have aligned with NIST SP 800-171 as a unified set of best practices expected for contractors to promote good cyber hygiene and safeguard sensitive information.
Register to Get Started
Complete this form to access the free cybersecurity assessment tool.
Completing the assessment will generate an executive report with valuable insights and customized security recommendations.
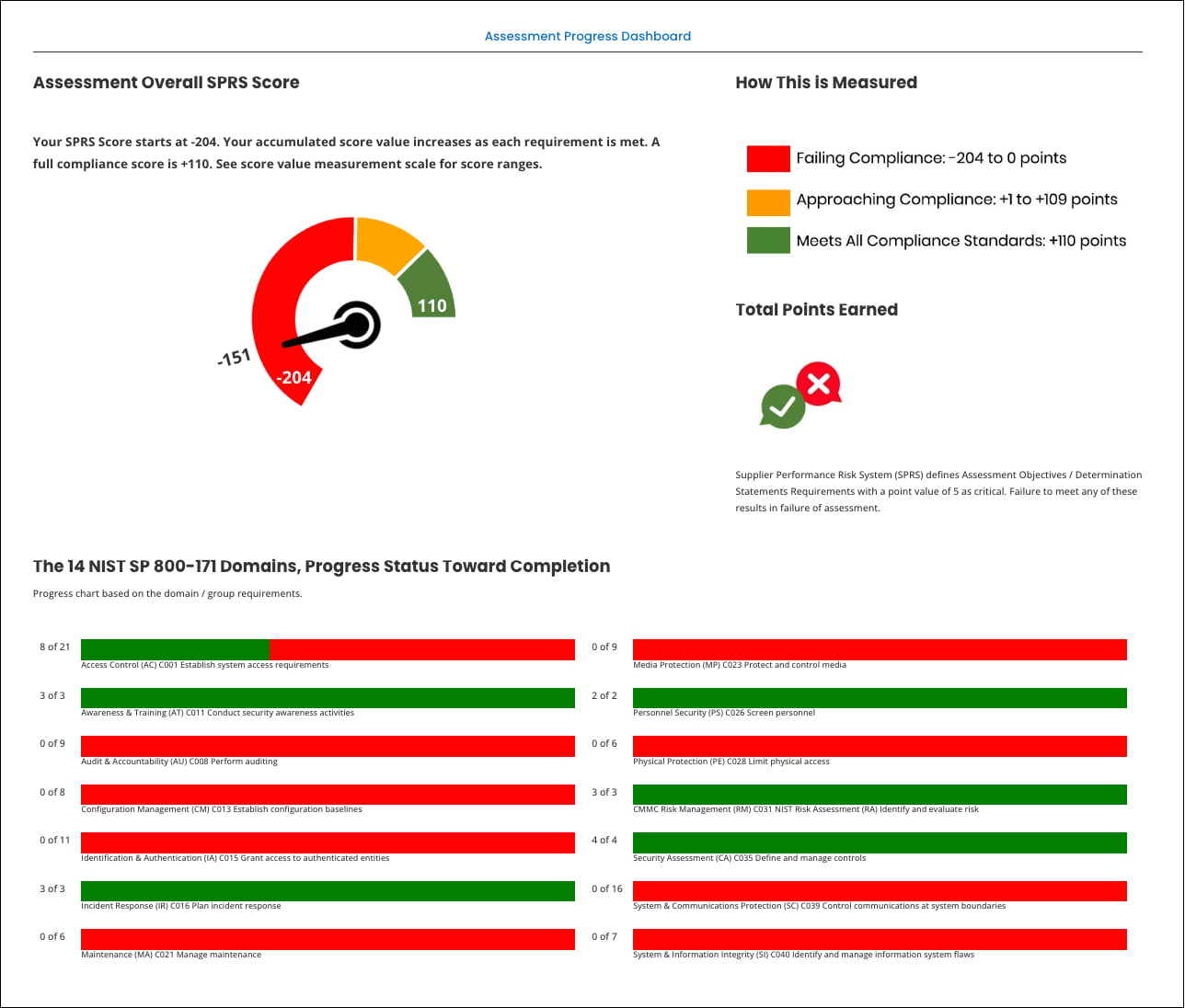
Progress Dashboard
Compliance with NIST 800-171A is a requirement for organizations that process or store CUI. It will be a core part of any contract or agreement between the US government and a contractor who is expected to handle CUI on their IT networks.
There is no certification body or official audit to determine a contractor’s adherence to the NIST 800-171 requirements. Organizations must self-assess and self-attest to compliance instead. Organizations perform an audit against the list of requirements found in the publication for all aspects of their network and systems that store or process CUI.
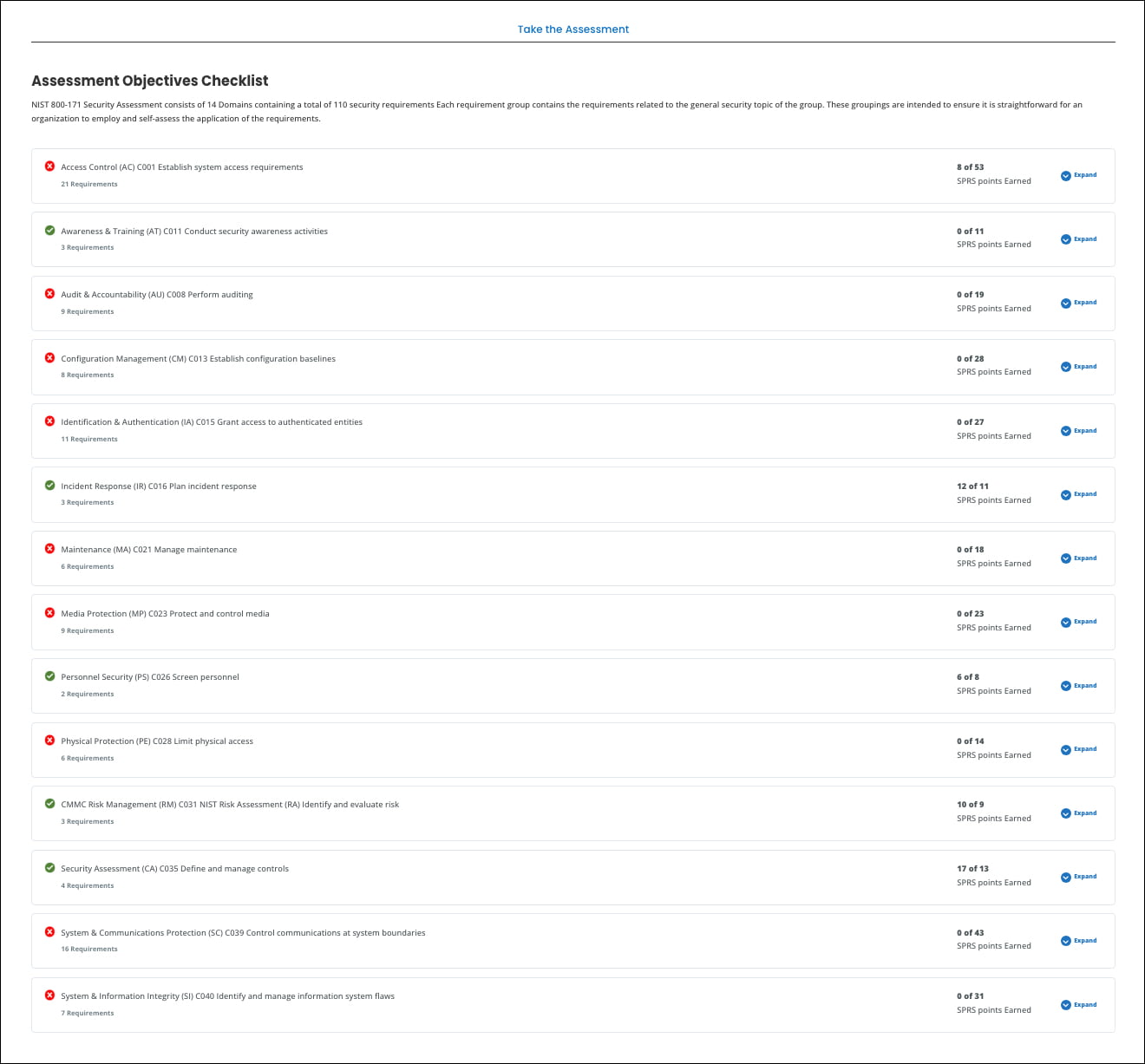
Audit and Compliance Checklist
NIST 800-171A compliance is proven through a process of self-assessment. There are 110 requirements that organizations need to meet in order to achieve compliance, which can seem daunting. But there is a clear process to executing a NIST 800-171 assessment.
The NIST 800-171 self-assessment is a complex task because it will audit all elements of an organization’s security systems and network that touch CUI. For this reason, preparation is key.
The assessment team should be assembled with input from both the core leadership team and the executive in charge of cybersecurity policies. Before beginning, an assessment plan should be created which outlines the timeframe, scope, and aims of the project.