CYBERSECURITY ASSESSMENT: REQUIREMENTS
NIST 800-171 Compliance
Complete this free cybersecurity assessment tool based on industry frameworks including the NIST Cybersecurity Framework to identify security concerns within your environment.
SPRS Dashboard
The 171Comply, Supplier Performance Risk System (SPRS) Dashboard is a means for an organization to self-assess and produce the SPRS score. 171Comply does not warrant the accuracy of the organization’s self-assessment. The score is the result of the organization’s self-assessment of their compliance to the listed Assessment Objectives. 171Comply has no influence, control, or responsibility for the accuracy or completeness of the organization’s self-assessment, and does not certify, approve, or validate any self-assessment.
NIST 800-171A Cybersecurity Assessment
Assessment Progress Dashboard
Assessment Overall SPRS Score
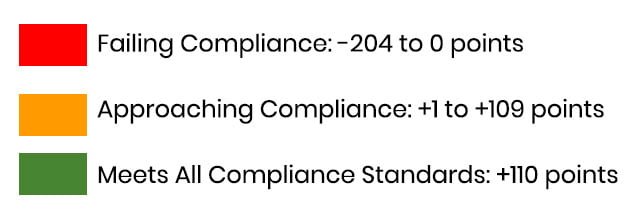
Your SPRS Score starts at -204. Your accumulated score value increases as each requirement is met. A full compliance score is +110. See score value measurement scale for score ranges.
How This is Measured
Total Points Earned

Supplier Performance Risk System (SPRS) defines Assessment Objectives / Determination Statements Requirements with a point value of 5 as critical. Failure to meet any of these results in failure of assessment.
The 14 NIST SP 800-171 Domains, Progress Status Toward Completion
Progress chart based on the domain / group requirements.
Take the Assessment
Assessment Objectives Checklist
NIST 800-171 Security Assessment consists of 14 Domains containing a total of 110 security requirements Each requirement group contains the requirements related to the general security topic of the group. These groupings are intended to ensure it is straightforward for an organization to employ and self-assess the application of the requirements.


